Working in the United States, when the FBI makes a security recommendation, you probably pay attention. Since February of 2020, the FBI has touted password phrases (aka passphrase) over passwords as more secure. Using long-formed phrases (aka content king) keeps hackers from figuring out your password – ranging from hours to more than your lifespan.
IN THE BEGINNING
For the most part, people use pet names, favorite celebrities, and birth dates, right-click in their browser to create ‘hard password’ options, and some folks just mash keys on their keyboard. There are those who feel their tech-savvy is elevated by the use of a password keeper. There is an advantage to a good password keeper that requires multi-factor authentication – the advantage of security at scale, with another organization responsible for layers and layers of security. But…
[Aside: if you didn’t know, LastPass was breached in DEC 2022. To date, 1Password and Bitwarden boast they haven’t been hacked – which is the equivalent of putting a target on them.]
If that password keeper doesn’t allow long-form password phrases, are you really being safe? If you are going to use a password manager, it would be wise to apply this conversation: content is king for passwords.
The tragedy behind common passwords is so comical it is worth checking out what the most common passwords were in 2022:
- 9 of the top 20 were a sequence of consecutive numbers (increasing or decreasing).
- 3 involved the word Qwerty – the top 6 letters of the top row of most English keyboards.
- DEFAULT and Password both made the list.
- Getting to reference “Iloveyou” in a FEB article feels apropos, but that was also in the top 20.
For reference: https://lmgtfy.app/?q=what+are+the+most+common+passwords+2022.
THEN EXCREMENT HIT THE OSCILLATING DEVICE
In 2022, Akamai saw over 60 billion credentials hacked and stuffed into websites for vulnerabilities. That number is up slightly from 100 billion over prior years (2018-2020). Cyber attacks are now a lucrative business vertical with a marketplace. There are set-and-forget tools for cracking passwords, searching for credential/password pairs on the dark web, and the like. We can thwart attacks by knowing what they are doing and how to make their work efforts miserable.
To keep this super simple, there is only one statistic to understand: how long it takes a hacker to brute force crack a single digit in a password.
The answer to that question, unfortunately, is instantly. A hacker can crack most 6-digit passwords instantly – with any combination of letters, numbers, symbols, etc. It doesn’t get complicated for hackers until the password is 10 characters long and contains numbers and both upper- and lowercase letters.
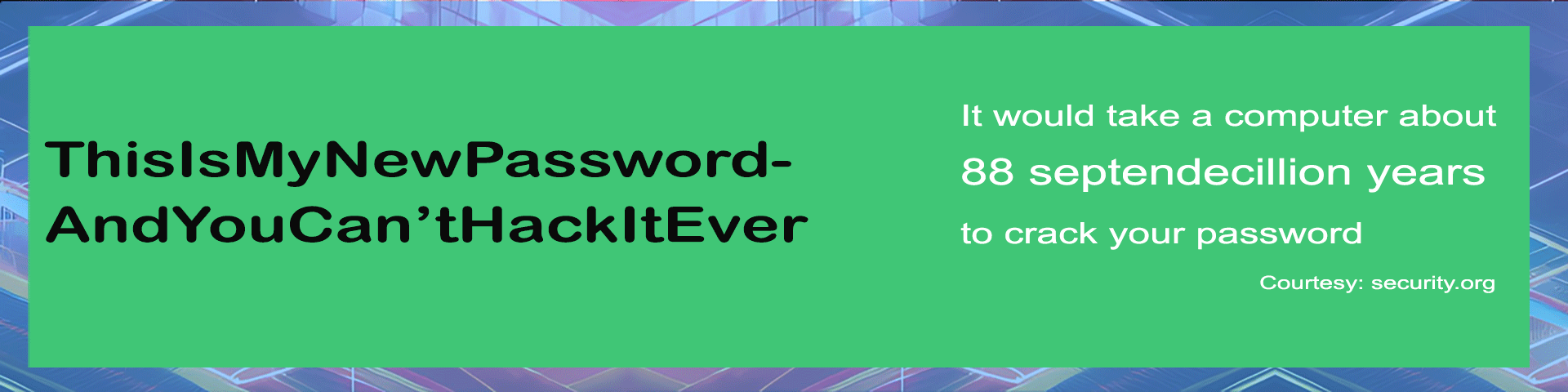
For fun, check out this password utility by Security.org that tells you approximately how long it will take a hacker to brute-force crack your password. This is based on current tools, the length of the password, and password complexity.
Not to spill the beans, but Security.org says the password iloveyou (it being February) would be cracked instantly. Anything in the top 20 used passwords is cracked instantly. Suffice it to say if you have a commonly used password, change it. Although, if you read for another 3 minutes, better password suggestions are provided.
For those that like to go super deep, here are a couple of pages on Brute Force and Hash Attacks:
- https://www.cloudflare.com/learning/bots/brute-force-attack/
- https://locker.io/blog/time-to-crack-a-password
- Re-reference from FBI (above): https://www.hstoday.us/subject-matter-areas/cybersecurity/fbi-password-length-much-more-important-than-password-complexity/
ENTER THE LONG-FORM PASSWORD
Let’s look at why and how the passphrases work best. This comes from my old-school statistics class.
- Tools can input 10+ trillion keys per second.
- There are 92 total options per password character (based on using all keys on a standard keyboard).
- A 6-character password using all keys has 606 billion combinations (92 x 92 x 92 x 92 x 92 x 92).
- Dividing that by 15T shows a fraction of a second to crack.
- Compare that to 6 characters, numbers only; there are only 1 million combinations.
- Compare that to 6 characters, letters only; there are about 20 billion combinations.
- Extrapolate that from 6-characters to 10-characters (9210), and crack time ranges from instantly (numbers only) up to 5 years (sounds better).
To summarize the math above, if you expand your passphrase out to 15 characters, no meaningful timeline on the hack is seen (one thousand years if you use lowercase letters). Just keeping this real, I don’t think anyone cares about a one-thousand-year-old password yet.
Doing the math isn’t necessary; Hive Systems updates metrics with great frequency and practices these exploits on modern equipment. A few years ago, hash hackers were only achieving 15 million keys per second. Currently, using graphic processing units (GPUs), tools can achieve up to 35 trillion keys per second.
HASH OUT THE END GAME
To close out, if you don’t have 15-character-long passwords across your important access points, it is time for some changes. One benefit of having a thousand-year-long passphrase is they don’t need to be changed with any frequency. In that FBI link (twice above), the recommendations from the National Institute of Standards and Technology (NIST) are shared, which basically tells everyone to use long passwords. It also tells administrators to 1) allow non-expiring, 2) screen passwords for known content, 3) don’t allow password hints, and 4) don’t lock out accounts. That last one will make users very happy (as long as they adopt long-form passwords). Number 3 prevents people from providing guidance towards their passphrase – where some folks will include/remove spaces from their actual password. 10 trillion characters per second don’t deserve hints to help crack a password.
Lastly, knowing that users have passwords that take one thousand years to crack provides a little breathing room for administrators. Instead of knee-jerk reactions blocking future intelligence, a little investigation can go a long way for future added defensive measures.